Building games of imperfect information with Aztec’s Noir language
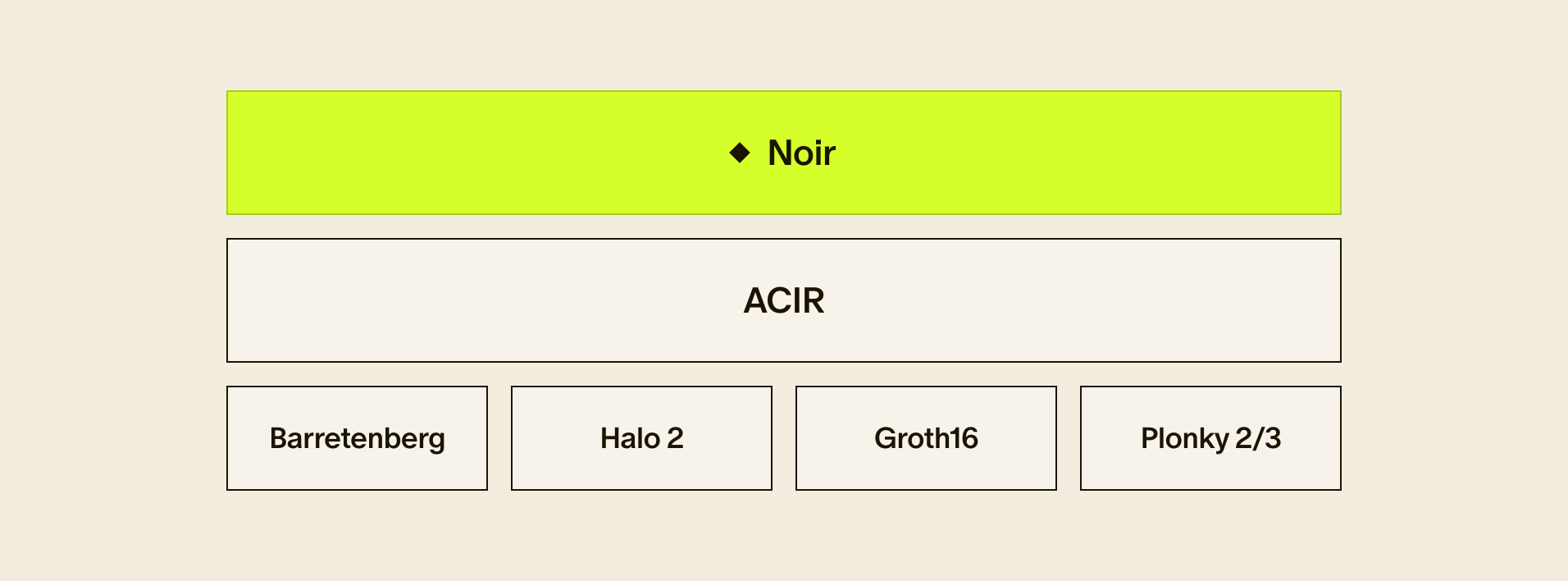
Noir was conceived of as an open-source, universal zero knowledge language. It was always meant to make the experience of developing in zero-knowledge much more accessible, by:
- having simple to read syntax that’s easy to reason about
- abstracting away cryptographic concepts and security considerations
- incorporating cryptographic libraries for commonly used crypto primitives
So when we heard about the Mach34 team and their work on BattleZips — a Battleship clone relying on zero-knowledge — we knew we had to work together.We met the Mach34 team after they placed at the ETHDenver 2022 hackathon with a Circom-written version of the classic Hasbro game Battleship.Shortly after we released Noir, they expressed ➡️ interest in rewriting Battlezips, providing us feedback, and creating a tutorial series on writing zk circuits and programs in Noir.
➡️ Watch the BattleZips-Noir YouTube series here.
We provided them an Aztec Grant in late 2022, and they were off to the races, culminating in showcasing the Noir-powered Battlezips running in the browser at our sponsored game night at ETHDenver 2023.
➡️ Play Battlezips in your browser.
Here’s an unabridged conversation with Mach34 on their experience building on Noir and what developers can expect building on the universal zk language.
A Noir-ish conversation with Mach34
Q: Tell us about BattleZips. How does the game use zero-knowledge cryptography?
A: BattleZips is a zero-knowledge implementation of the popular board game Battleship that uses proofs to shield ship positions. While this is by no means an original idea for a zero-knowledge application, Battleships was chosen as it is a simple but complete example of integrating arbitrary business logic in zero knowledge circuits.
By settling zero knowledge proofs in smart contracts, we can create novel digital and economic interactions that make the existing role of Information Escrow by third parties obsolete. BattleZips helped us understand how to apply zero knowledge proofs, and we hope the BattleZips-Noir course gives you the same advantages!
Q: What inspired you to start Mach 34 and develop BattleZips? Why explore Noir?
A: BattleZips marked the beginning of our journey into zero-knowledge cryptography and expanded our horizon on where this technology could be applied in real world use cases.
This is one of the factors that lead us to creating Mach 34. Mach 34 is a Web3 and ZK Software Consultancy. We chose to focus on mastering the web3 tech stack for the sake of expertise rather than a specific application. This enables us to explore any industry ripe for decentralization, growing our overall experience with the enterprise of web3.
Corporations and governments alike habitually abuse the authoritative topology of web2 networks; as Web3/ ZK Consultants, we have the means and the desire to help innovators usurp centralized processes and give sovereignty in cyberspace back to the users.
It is crucial that we stay up to date with the latest trends in this fast developing space to ensure we provide superior expertise to clients. Our prior experience writing proofs demonstrated to us that there is a significant variation between the different tools that exist, how rapidly they can be applied to an engineering problem, and what they accomplish. This led us to explore Noir upon its official release and see how it differentiated itself from pre-existing alternatives.
Q: How did you find the ease of usability of Noir compared to other zero-knowledge domain specific languages you’ve worked with?
A: Prior to Noir we used the Circom language and the Halo 2 proving system written in Rust. Proceeding from a first look at the Noir documentation to writing circuits was a fairly quick and straightforward process.
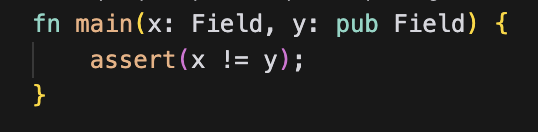
We thought that Noir lived up to most of what it promised in its introductory medium post. If one were to begin learning Noir without wanting to get bogged down in learning the inner workings of ZK and how circuits translate to proofs then they could certainly do so. It does a good job of abstracting away from the more complex aspects of the topic.
One thing that could improve the developer experience is ensuring that the nargo command-line tool and the Aztec NPM packages compile the same Noir version. This is an issue we ran into mid way through the development process that resulted in a refactor to ensure we could test our circuits with the Aztec NPM packages.
Q: As a full-stack development shop, how has the process of incorporating zk-cryptography changed the way you approach software development projects?
A: Our interest in zero-knowledge cryptography was one of the driving factors for starting Mach 34. Historically and to this day, one of the most sought after skills in the web3 space is the ability to write smart contracts.
Similarly as the past few years have shown, we believe enabling privacy and scalability in web3 applications is only going to become more and sought after and ultimately a necessity. In anticipation of this we have positioned ourselves at Mach 34 to have the skills and expertise necessary to help companies engineer ZK solutions.
Q: What kind of impact do you think Noir and other zero-knowledge domain specific languages will have on the broader software development community? Where do you see the industry going?
A: Noir and other ZK DSLs play a pivotal role in the proliferation of zero-knowledge cryptography by abstracting away from the underlying cryptographic principles.
As history shows, abstraction is absolutely necessary for any technology to become widely adopted. If engineers were never able to design high level programming languages from low-level opcodes then we would have far fewer and less effective software developers than we do today.
Once the complexity and thought is removed from the underlying components that make zero-knowledge cryptography possible in the first place, engineers have more time to think about applications that would benefit from ZK. It looks like we are about to enter an exciting phase where we will start to see more examples of the technology applied to real world use cases.
Q: What advice would you give to developers who are interested in learning more about zero-knowledge cryptography and how to use it in their projects?
A: This is definitely an exciting space to get involved in given it is still very much in its infancy. It is poised to solve issues related to privacy and scalability in public blockchains, as well as contexts out of web3 where there is currently a lack of much needed privacy.
This being said, resources for learning are still sparse and those that exist often have a technical complexity that can make them hard to digest. It can take quite a bit of patience and perseverance to become acclimated to this space but it is well worth the effort given that you are one of the individuals pioneering the ecosystem.
If you are a developer that has an interest in getting started in ZK then I think reading some high-level introductory materials would be a good starting point.
After a basic understanding is gained on the topic then exploring a DSL like Circom or Noir to write a simple circuit would be a beneficial next step.
Once it becomes clearer to you what can be accomplished and what tools are at your disposal then really the limit is what you can ideate. The cool thing is that there is still so much room for novel innovation that it could very well be the case no one has thought of your idea yet. Don’t sit idle and wait for things to develop further! Now is a great time to jump in!
Q: Are there any upcoming projects at Mach 34 that you can share with us that utilize zero-knowledge cryptography or other cutting-edge technologies?
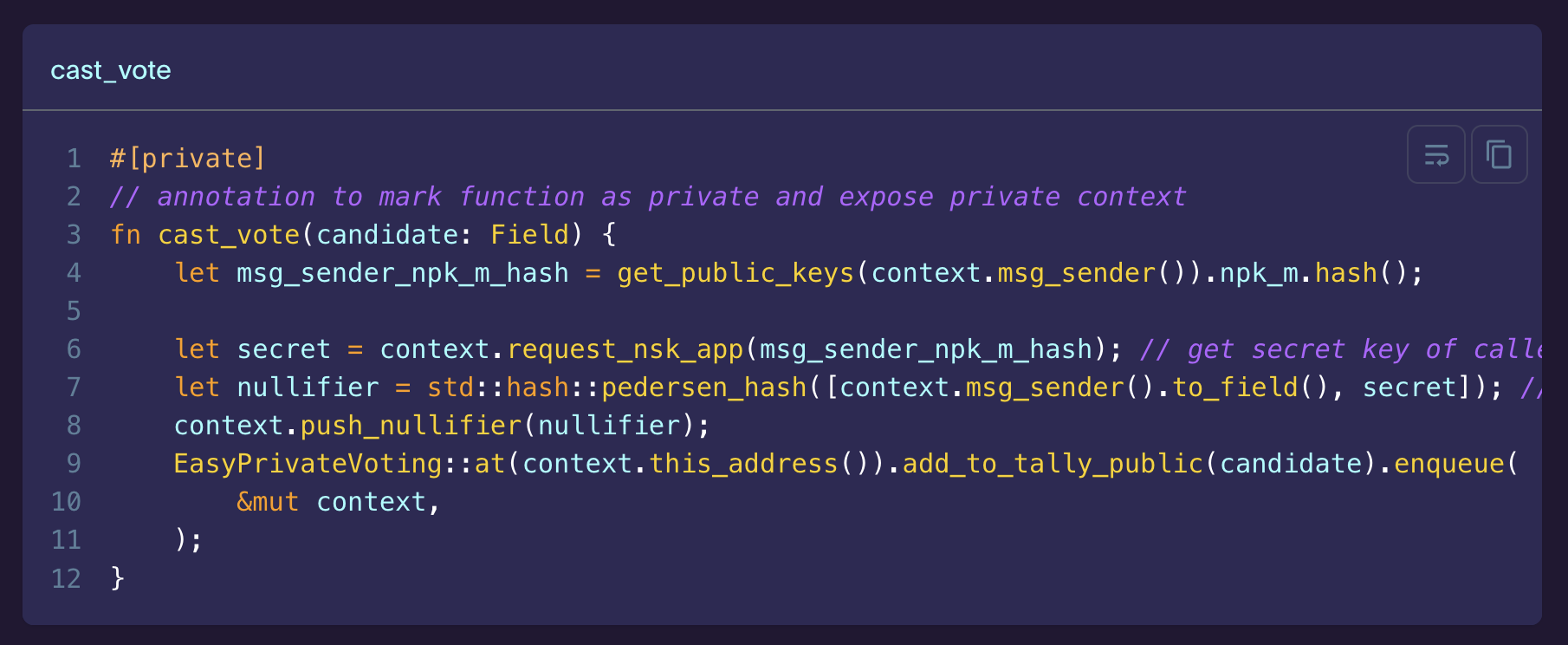
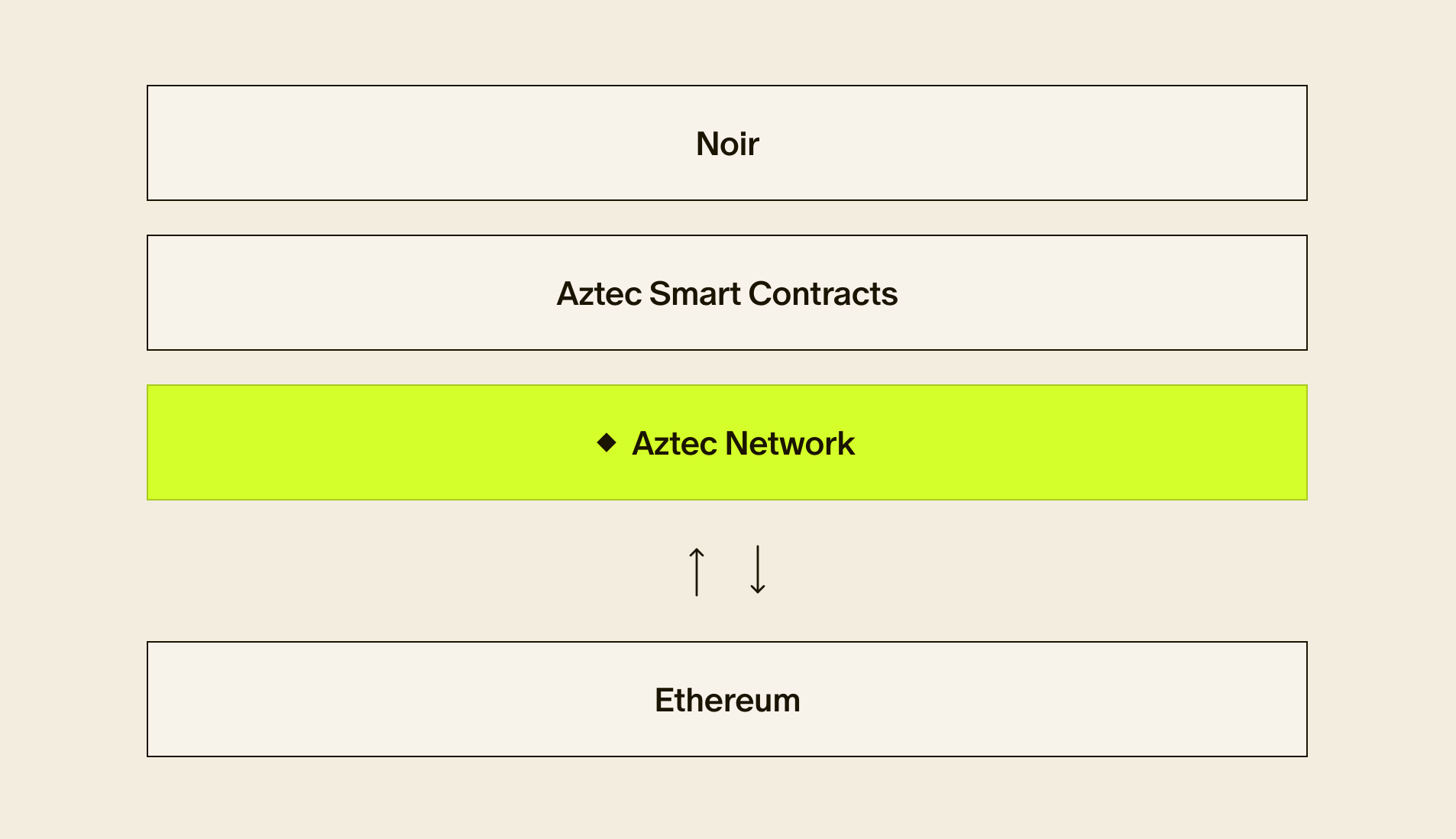
A: Mach 34 has been researching and working towards constructing a “Zero-Knowledge State Channel”. While rollups offer fantastic scalability, we were put off by the need for a sequencer. Furthermore, aside from Aztec Connect and a few others, ZK Rollups do not have any private state. Thus, we began to explore how state channels might be repurposed with zero knowledge.
To open a ZK State Channel, parties will agree on the terms of the execution (like a smart contract). The channel initialization dictates what steps can be taken next, and by whom. Rather than posting every transaction on-chain, a state object is recursively built off-chain.
While previous state channel constructions had optimistic trust assumptions, we can leverage ZK to perform verifiable computations that have instant, trustless finality. Once a state channel has reached an end condition, the entire state execution is notarized by posting the state channel proof on-chain for all nodes to verify in zero knowledge.
This final proof further employs zero knowledge to hide most of the intermediate state; only pre-determined derived metrics or public outputs are made publicly available on-chain.
This has many interesting use-cases; we plan to demonstrate how this construction is useful for credit scoring by adding ELO scores to the State Channel version of BattleZips. This provides a verifiable metric that scores the performance of an individual without revealing any of their in-game moves.
We envision countless use-cases for ZK State Channels across all segments of web3. Undoubtedly, there are use-cases that we haven’t thought of. For this reason, all of our work on ZK State Channels is free and open source. While we intend to utilize the infrastructure for profit, we want to make sure that all possibilities are explored in service of the best possible future for web3 developers and users.
Q: What are some use cases you’re excited for?
A: One area of exciting potential outside of blockchain is how zero-knowledge can transform personal identification.
When providing personal ID, the majority of the time more information is conveyed than necessary. Proving one is of a legal drinking age need only confirm the person is above 21 years of age, yet sharing the ID divulges information such as street address and name.
Using zero knowledge proofs conceivably one could prove they are at least 21 without having to provide additional information. Another example is having to provide a social security number in a KYC process. Leaking a SSN number can have catastrophic consequences so one would prefer this is done as infrequently as possible. With ZK proofs instead one could prove they bear a SSN number without needing to reveal exactly what theirs is.
Explore the BattleZips project
We’re thrilled that the Mach34 team have done such a deep and candid dive into Noir’s capabilities, and their feedback has been invaluable.For developers interested in building on Noir, check out their well-documented BattleZips repo.
➡️ Explore the BattleZips Github repo and codebase.
Build on Noir
Interested in building zero-knowledge applications on Noir — or contributing to the open-source project?
- Get started in our docs here.
- Join Noir developer office hours every Thursday at 10am ET.
- And jump into our Discord and continue the conversation with us in the #noir channel.
Join Us
We’re always looking for talented engineers, cryptographers, and businesspeople to join Aztec. We are committed to bringing encryption to blockchain through our encrypted zkRollup, and we’ve raised over $125 million from the best investors in crypto, including a16z and Paradigm to do so. Come onboard.