Last week, PSE published an insightful and comprehensive user-research piece on private transfers on Ethereum. They interviewed 38 teams in the space and asked what's broken, what's missing, what builders wish they had. The list reads like a wishlist of features every privacy app on L1 is currently trying to engineer towards. It's the kind of rigorous, builder-grounded research the privacy ecosystem has needed.
We read the list. It's the list we've been building against for years.
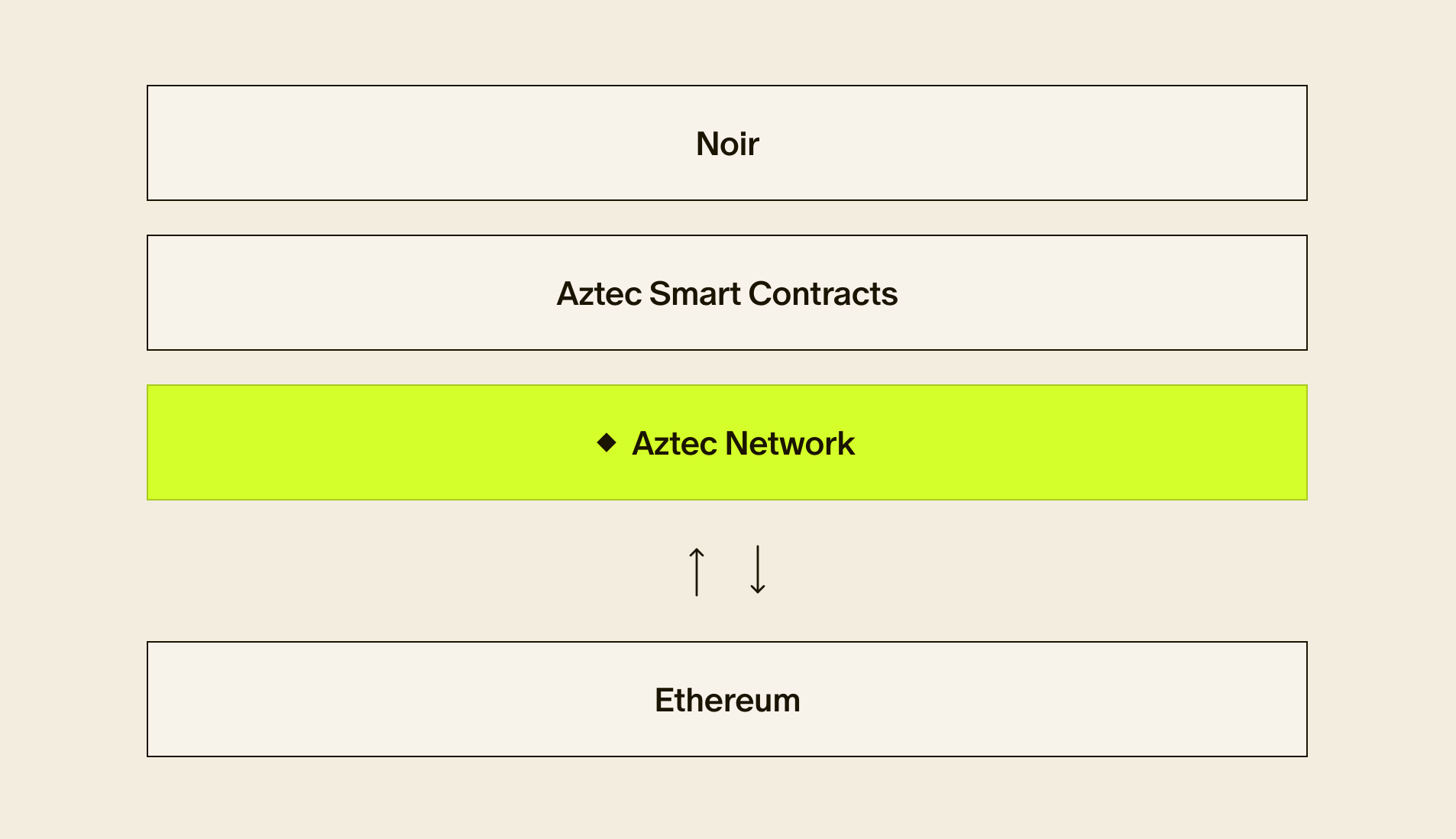
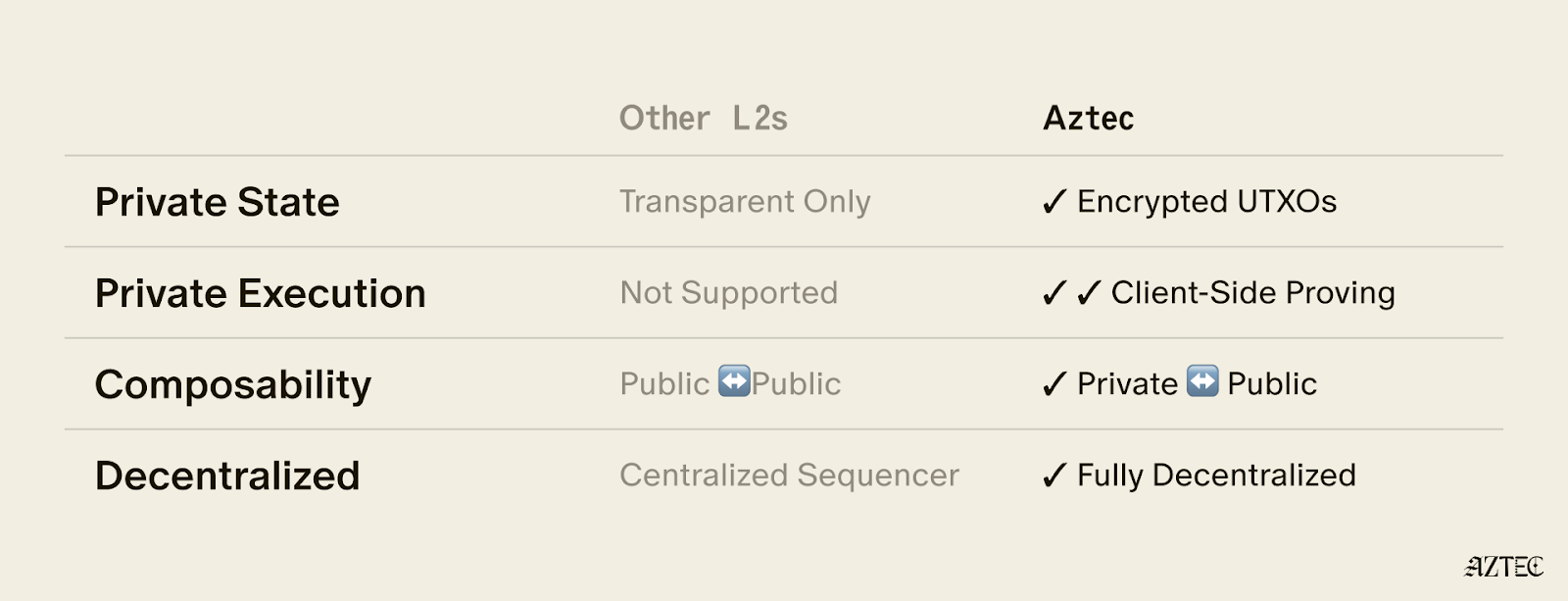
Aztec solves all of these problems. Every requested feature already lives on Aztec. The proving system, the private contract language, the decentralized network, the privacy wallet architecture, the key model, the snark-friendliness: all of Aztec was built against this list before it was a list.
What follows is a walkthrough. For each of PSE's top technical findings, here's the feature builders are asking for, and how it works on Aztec today.
TL;DR
- Slow client-side ZK proving: Aztec's client-side proving system (Chonk) is optimized specifically for fast recursive proving on resource-constrained devices such as phones (and even in the browser).
- Expensive L1 proof verification: Aztec amortises the gas costs of L1 verification across thousands of users per rollup. Instead of “millions of gas per user” it costs hundreds of gas; that’s pennies per user transaction.
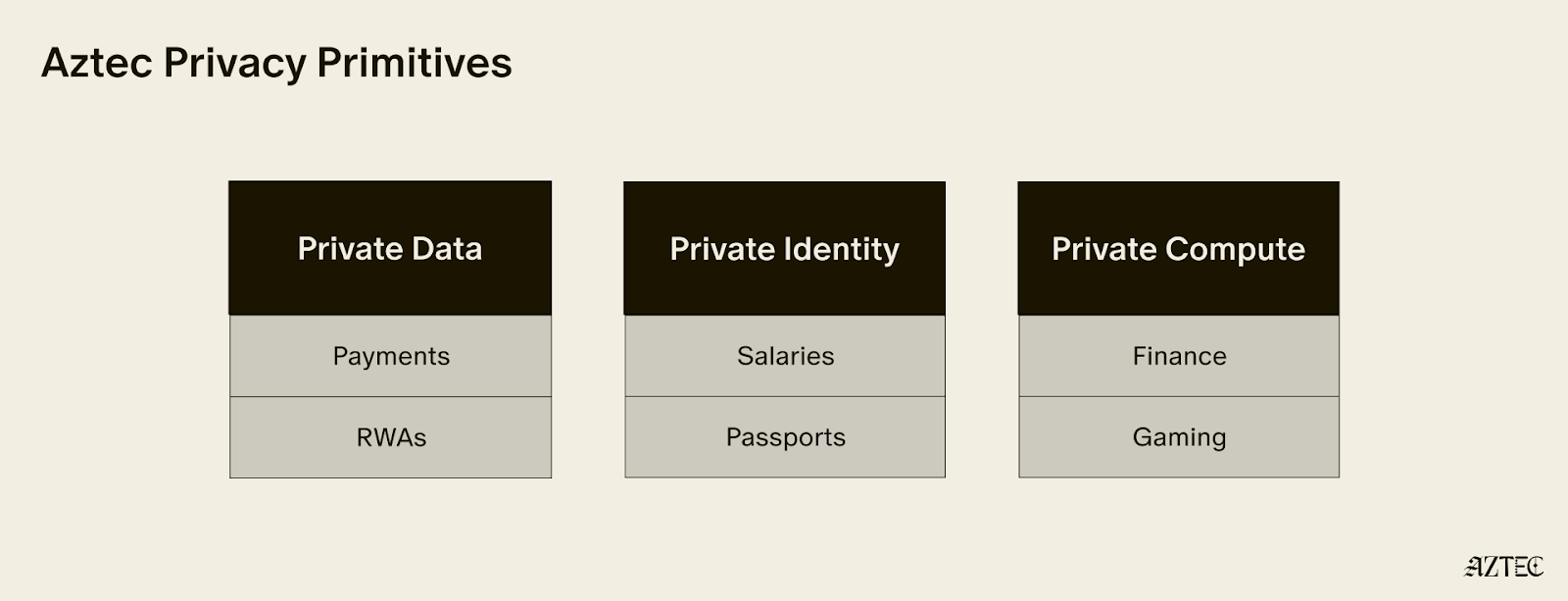
- DeFi composability with private state: Private token contracts on Aztec can be unshielded to easily interact with Ethereum DeFi contracts, and the resulting state can be shielded, without leaking who did the interaction. Or you can just design composable private DeFi contracts within Aztec.
- Deposit/withdrawal leakage: Aztec isn’t a basic shielded pool, so users don’t need to keep withdrawing to do useful things. Users can use their funds within private smart contracts. Privacy leakage doesn’t happen if all transaction activity stays in private-land.
- No native wallet support: Of course Ethereum wallets don’t natively support privacy; Ethereum doesn’t have native privacy. There are a huge number of new concepts that are needed to design a private smart contract wallet. Aztec wallets are built from the ground up to enable a rich private onchain experience.
- Reliance on external networks, TEEs, FHE, and relayers: The private and public execution environments of Aztec aren't reliant on external networks. Aztec is a fully decentralised L2, without these centralisation concerns.
- Keccak is inefficient inside ZK circuits: The entire Aztec protocol uses Poseidon2, so complex private txs are rapid to prove on a phone.
- Slow private state sync: Brute-force scanning of the entire chain’s history is not necessary. Aztec's tagging scheme lets recipients pinpoint their notes in seconds from a shared secret.
- Fragmented privacy sets: All private smart contracts on Aztec share one global note tree and one global nullifier tree. All network activity contributes to and draws from a single privacy set.
- No tooling or standards for private contracts: Aztec has a huge suite of tools to ship private contracts. Noir, a smart contract framework, a private state manager, a keystore, the PXE for executing contracts locally, a JS SDK, testing frameworks, local test networks, a CLI, and a slew of advanced private contract standards.
1. ZK proof generation time on user devices
Ethereum Problem: Proof generation is too slow on user devices, especially mobile. Elliptic-curve pairing operations are a specific bottleneck. Server-side proving is a censorship and privacy leak vector. Sub-second proving was the stated threshold.
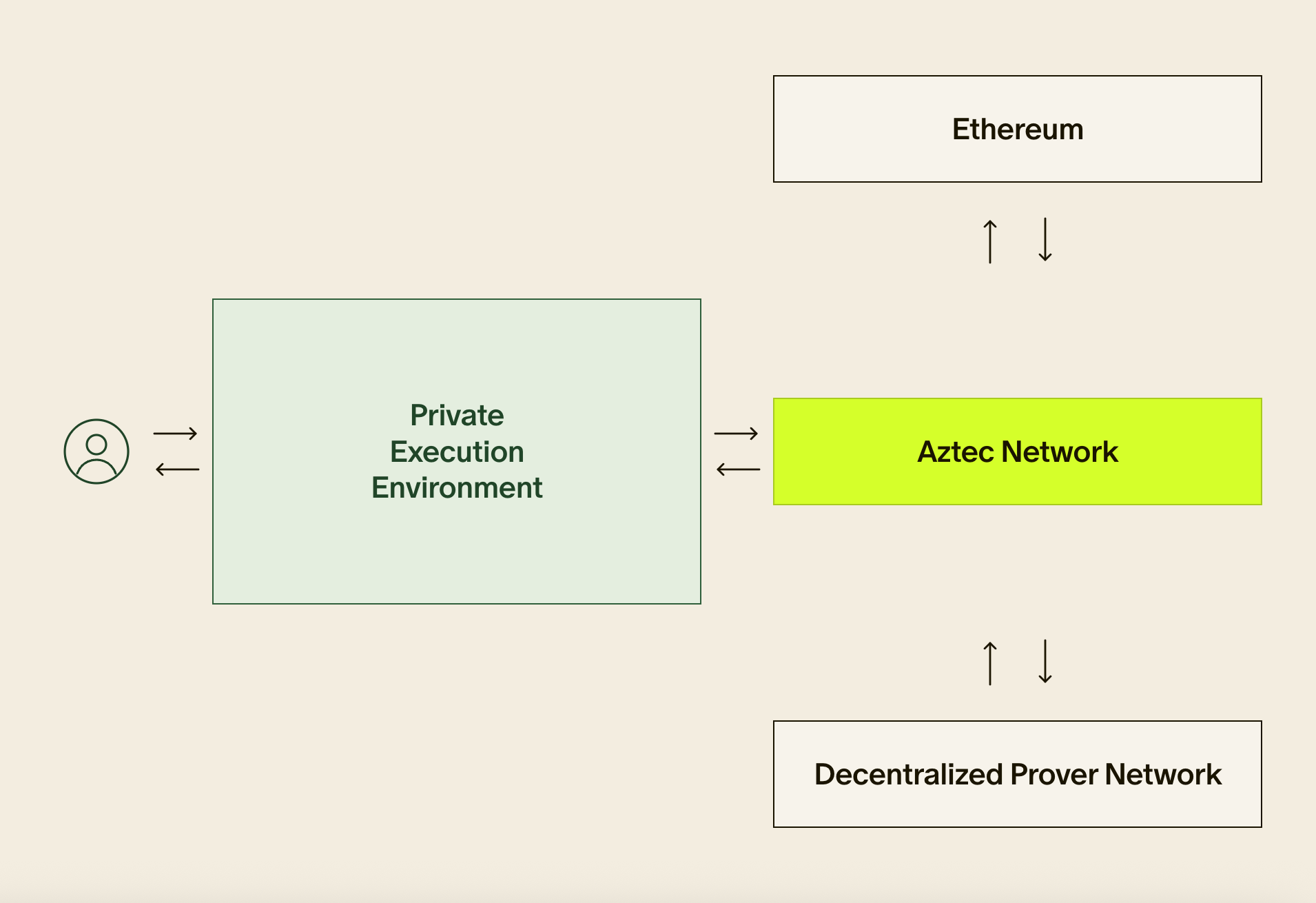
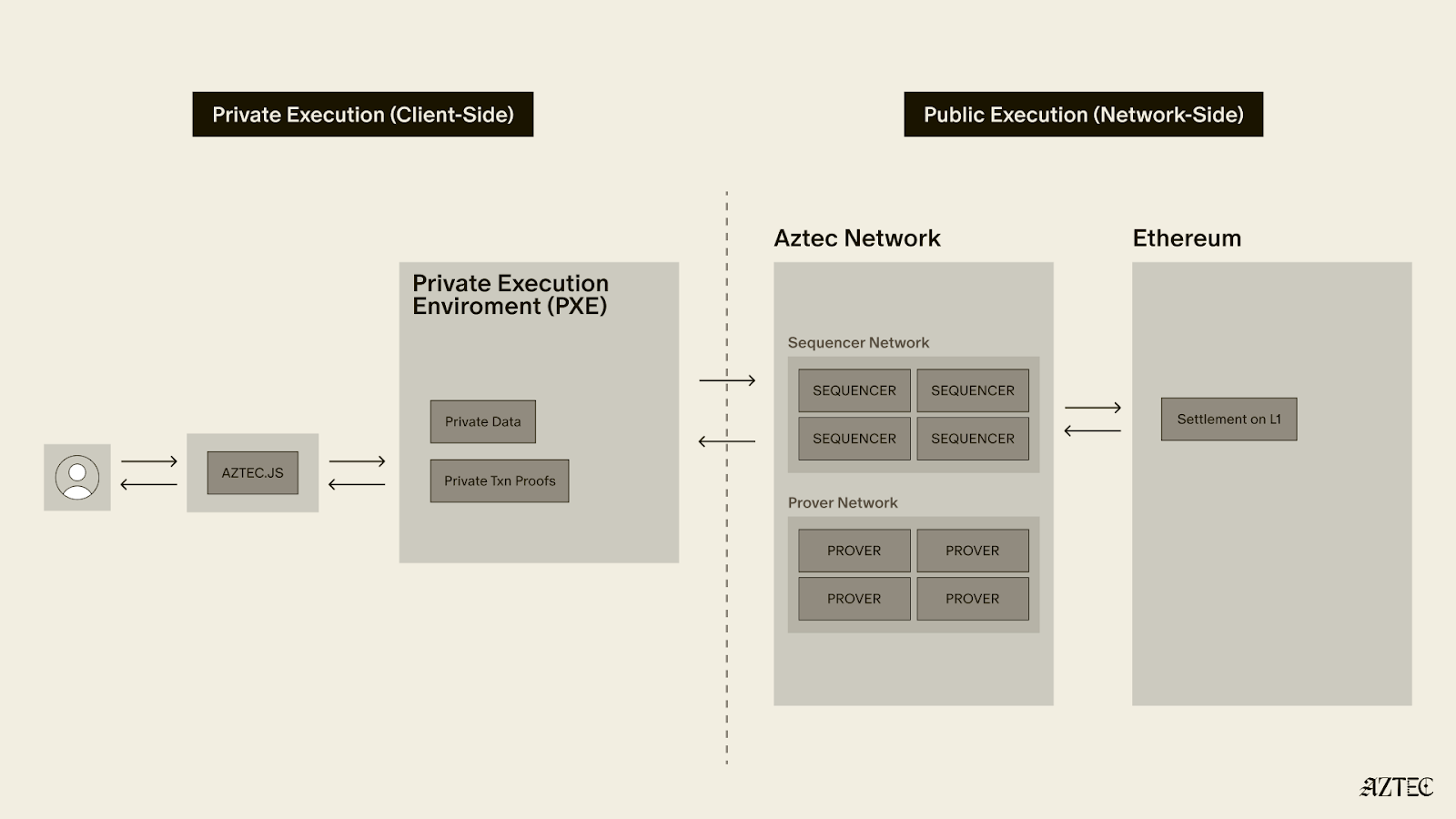
Aztec solution: Proving on Aztec runs locally in the PXE (Private eXecution Environment, pronounced "pixie"), so no data ever leaves the user's device. Chonk, our client-side zk proving system, is ruthlessly optimised for fast recursive proving on low-memory devices like phones, native and in-browser. Years of optimization have already gone in, and we're still finding more. It’s best in class and we haven’t even merged-in GPU acceleration yet!
The slow pairing checks that PSE's interviewees called out as a bottleneck aren’t a problem with Aztec; pairings are simply batched together and deferred away from the user's device, handled by the more powerful network instead, without leaking any information. With such a powerful local prover, there’s little need to outsource proving to an untrusted party.
2. ZK proof verification gas on L1
Ethereum Problem: Verifying a ZK proof on Ethereum is prohibitively expensive. A Groth16 proof for a private transfer costs several hundred thousand L1 gas. A Halo2 (KZG Plonk) proof can cost approximately one million gas
Aztec solution: Aztec amortises L1 verification gas across all transactions in the rollup. At current network throughput, that cost is split across roughly 2,000 users per proof. Later this year, it’s slated to be split across ~20,000. Rollup costs are also partially subsidised by Aztec block rewards.
Net result: hundreds of L1 gas per user instead of millions. Plus cheap L2 gas. The user pays pennies for an Aztec transaction.
3. DeFi composability with private state
Ethereum Problem: Wrapping and unwrapping tokens leaks privacy and breaks composability. Smart contracts can't easily interact with encrypted balances. Private state is isolated; contract state is normally shared.
Aztec solution: Private state is not isolated on Aztec. The private state of one contract can be composed with that of another. This can unlock new privacy-preserving DeFi patterns directly on Aztec.
A single private transaction can call a stack of private functions across multiple contracts, with private inputs, private state transitions, and privacy over which functions were even executed and how many. Observers see that a transaction landed. They do not see what happened inside it. Stew on that for a second: a call stack of nested private functions across contracts written by different developers, each causing state transitions, all completely private.
Aztec also runs public functions, similar to Ethereum, inside the same smart contract, so you can build existing DeFi primitives on Aztec.
For Ethereum DeFi specifically, Aztec has a tidy L1-to-L2 messaging layer. Private balances can be unshielded to interact with L1 protocols and shielded back, without leaking who did the interaction and without leaky public gas payments. And for private DeFi primitives that need genuinely shared private state (state nobody knows the value of, but which anyone can mutate), people have built Aztec contracts that compose conventional Aztec private state with co-snark or FHE sidecars.
Private and public state are peers inside a single Aztec smart contract. Builders mix and match.
4. Deposit/withdrawal privacy leakage
Ethereum Problem: Entry and exit points are the dominant privacy leak, not the protocol itself. Depositing and quickly withdrawing makes identity analysis trivial.
Aztec solution: The main fix is to stop crossing the boundary so often. (Or even if you do cross the boundary, Aztec has leakage protections).
Imagine if thousands of private smart contracts lived on the same network and could call each other without leaking which contracts were called, which arguments were passed, or what was returned. Imagine they all shared one global note tree and one global nullifier tree. That's Aztec. Once funds are inside, users don't need to keep crossing the private/public boundary to do useful things: Aztec is its own rich environment for composable, private execution of smart contracts.
Even when a private function does need to call a public function – be it an L1 DeFi contract, or a native public function within Aztec – the developer controls the information they reveal; not the protocol. The call can even be "incognito" to hide msg_sender. A single environment for many private apps to thrive also means re-usable tooling for builders.
5. Lack of native wallet support
Ethereum Problem: Privacy features (per-dapp addresses, private transfers) aren't natively integrated into major wallets. Reliance on dapp-specific UIs damages UX.
Aztec solution: Ethereum wallets weren't built for any of this, and they don't need to be: the chain underneath them has no private state to protect. Aztec wallets are an entirely new category of software.
Aztec wallets are able to manage all these new privacy-centric concepts:
- Authorize your transactions however you want, without revealing your identity to the world. Native account abstraction lets you choose any auth scheme you like, and that choice doesn't expose who you are.
- Hold multiple specialized privacy keys. Distinct nullifier, viewing, and efficient message-signing keys.
- Keep your full private state on your own device. An encrypted local database holds your notes and nullifiers (siloed by private contract address), along with private data, private messages, shared secrets, and private contract bytecode.
- Fine-grained contract access control for your private data.. Access permissions for contracts to read your private data are granular and revocable, rather than all-or-nothing.
- Run private contracts without cross-contract interference. Built-in protections can stop malicious private contracts from reading or manipulating the private state of other contracts.
- Establish shared secrets with your counterparties. Wallets can support both on-chain and off-chain methods for setting these up.
- Catch privacy leaks before you sign. Pre-flight transaction privacy analysis warns when your data might be leaked via public args, msg_sender, fee payment, or even through the shape of the tx.
- Make your tx look like every other tx on the network. Random padding is added to notes, nullifiers, and logs, and gas settings, anchor blocks, and inclusion deadlines are randomized so every tx blends in with the crowd.
- Submit transactions privately to the network. Txns can be submitted to the network through a private submission path.
- Pay fees through generic private fee paymasters. This gives users convenience and enables experimentation over the best private token contract designs for different use cases.
- Use your wallet to gatekeep which frontends can access which private data . Apps shouldn’t have unfettered access to everything; a wallet needs to protect users’ private data..
- Get post-quantum hygiene warnings. Wallets are able to flag risky patterns around address reuse and ephemeral-key broadcasts.
Aztec wallets are in active development, and this is an area where we expect many teams to build different wallets that are customized to various user needs. An early wallet is already baked into the protocol for developers to start using today.
6. Reliance on relayers, FHE coprocessors, and TEEs
Ethereum Problem: Encrypted tokens and many privacy protocols depend on external networks for encryption, decryption, or relaying. Threshold-decryption committees and TEE hardware vendors are added trust assumptions on top of the chain itself.
Aztec solution: Aztec's private and public execution environments are not reliant on external networks. Aztec is its own decentralised network: ~4,000 validators stake on it, block proposers are randomly selected, a random committee attests, and a decentralised set of provers proves the rollup's execution. Validity is ultimately backed by cryptographic proofs settled on Ethereum.
External networks (co-snark networks, TEEs, MPC or FHE sidecars) become an opt-in choice for the specific case of private shared state. The trust tradeoffs there are something the contract developer signs up for explicitly, not a tax every user pays on every transaction by default.
7. Hash function inefficiency inside ZK circuits
Ethereum Problem: Keccak is inefficient to prove inside ZK circuits. There is no native support for a ZK-friendly hash like Poseidon.
Aztec solution: Poseidon2 is enshrined across the entire Aztec protocol, for rapid proving of every tx. Every Aztec state tree, the proving system, the innards of the protocol; everywhere. Reading and writing state inside a circuit is as cheap as it gets.
Keccak, SHA, and Blake hashes are still available through optimised Noir libraries when contracts need them for L1 interoperability. The default is ZK-friendly; the L1-friendly hashes are there when you reach for them.
8. Private state synchronisation
Ethereum Problem: Syncing private state (scanning for incoming notes and events) is a client-side bottleneck. Users wait for scans to complete before seeing their balance. Tachyon-style oblivious sync was cited as a path forward.
Aztec solution: Brute-force syncing of private state is rarely needed. Most real-world use cases involve a sender and recipient who can establish a shared secret offchain first.
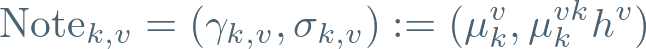
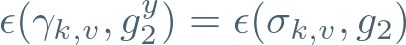
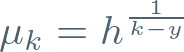
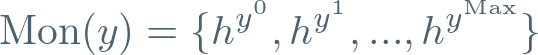
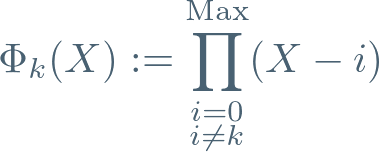
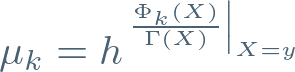
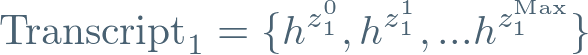
From that shared secret, both parties can derive a sequence of random-looking “tags”. Each encrypted note log is prepended with the next tag in the sequence. The recipient already knows the next tag, so they know exactly what to query. Note discovery happens in seconds, not minutes. The scheme slots cleanly into PIR or mixnet approaches for extra privacy on the query itself, and smart contracts that don't trust senders to use the correct tag can just constrain it inside the circuit.
That’s not to say that Aztec requires interactivity between all senders and recipients. For genuinely non-interactive use cases (recipient can't talk to the sender before the transfer), Aztec enables devs to customize both their log emission and their note-discovery logic however they like. (Aztec also has ways to speed up the brute-force scanning approach from "scan the whole chain" to "scan a tiny subset of non-interactive handshake txs"
9. Fragmented privacy sets
Ethereum Problem: Shielded pools are fragmented across dapps and chains, reducing the effective privacy set for all users. Each new privacy protocol must bootstrap its own.
Aztec solution: There is one global note tree and one global nullifier tree on Aztec, shared by every smart contract on the network. Every private app contributes to and draws from the same privacy set. No per-app bootstrap. No walled gardens.
Private payments, private swaps, lending, payroll, treasury, identity attestations: all of them land in the same global commitment set, by construction.
10. Tooling and standards for private contracts
Ethereum Problem: Ethereum developer tooling lacks support for private transfers and private state. Standards for private tokens, compliance, and wallet interactions are missing. Many privacy teams are small, with short runway and expensive audits.
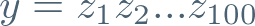
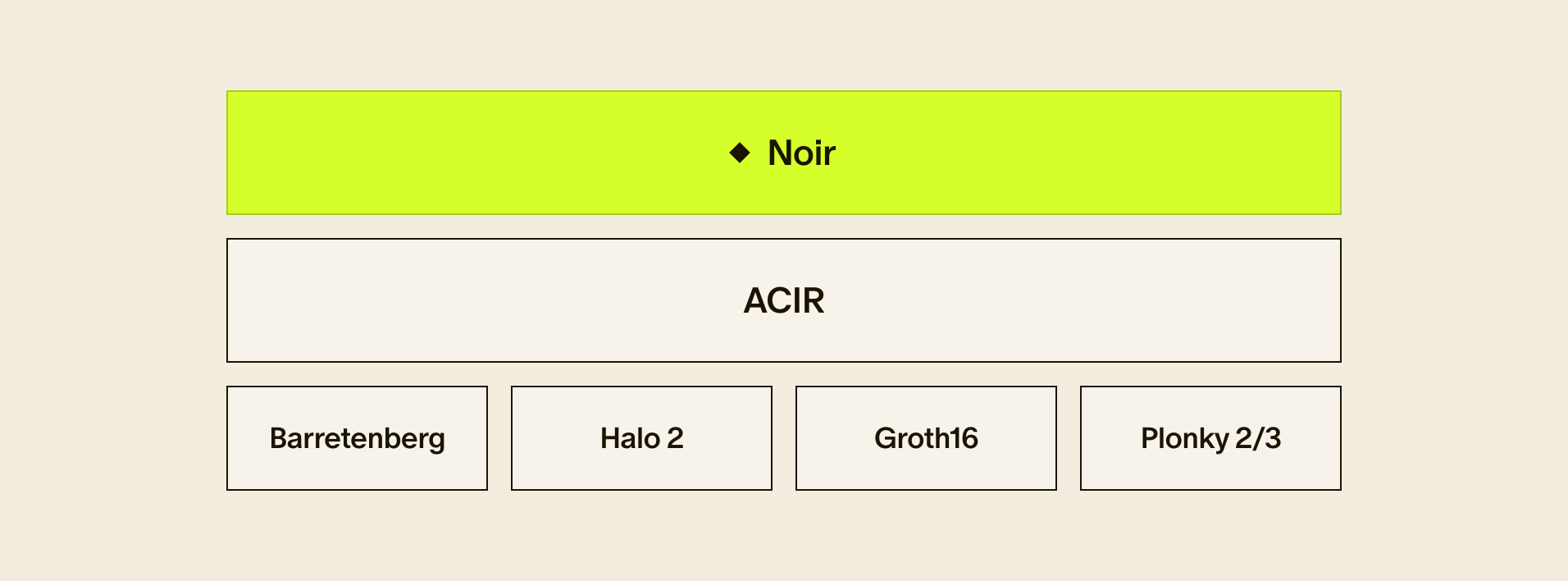
Aztec solution: Aztec ships the full toolchain for private contracts: Noir for writing private logic, the Aztec smart contract framework with macros that hide the protocol mess so devs can focus on app logic, the PXE for keys / state / syncing / proof generation, a JS SDK, a local node for testing, a CLI, and a real, live, decentralised L2.
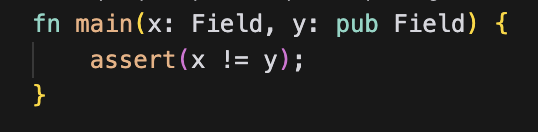
The mental overhead of building a privacy protocol on Aztec collapses to "just write the app logic." Here is an example of a complete private transfer function on Aztec:
#[authorize_once("from", "authwit_nonce")]
#[external("private")]
fn transfer_in_private(from: AztecAddress, to: AztecAddress, amount: u128, authwit_nonce: Field) {
self.storage.balances.at(from).sub(amount).deliver(MessageDelivery.ONCHAIN_CONSTRAINED);
self.storage.balances.at(to).add(amount).deliver(MessageDelivery.ONCHAIN_CONSTRAINED);
}
Look at how simple that is.
A two-line function body.
Two lines.
Aztec takes care of the rest.
Behind those #[...] macros, the framework handles: caller authorisation, note syncing, fetching notes from the user's private db, Merkle membership proofs against the global note tree, safe nullifier creation (without leaking master secrets to the circuit), randomness for new notes, encrypted ciphertext generation, log tagging for fast recipient discovery, and public-input population. The PXE handles key management, private state, and proof generation. The smart contract itself contains its own message-processing logic for log discovery, decryption, and storage on the recipient side.
If you want whitelists, blacklists, association sets, custom tx authorisation, viewing-key hierarchies, temporary view access, selective disclosure to specific counterparties, just import a Noir library. Want something more adventurous than private payments? Same toolchain.
What this adds up to
PSE's findings are not ten unrelated bugs. They're the same problem refracted ten ways: privacy retrofitted onto a chain that was not designed for it yields bad tradeoffs.
Aztec was designed against this list before it was a list. One global note tree and one global nullifier tree. Private and public state inside the same contract. Compose calls between private contracts without leaking anything. Fast client-side proving on phones via Chonk. Snark-friendliness everywhere. Rollup-amortised L1 gas costs, fractions of a cent per user. Native account abstraction with private fee paymasters. No painfully slow private state syncing: a tagging-based note discovery scheme that runs in seconds. An entirely new category of wallet that treats privacy as a first-class concern. Simple, high-level smart contract syntax that collapses a basic private token transfer function into two lines.
There were 10 privacy features Ethereum devs wanted, all of them live on Aztec. The infrastructure is in place. Build the thing.
Aztec is the blockchain that solved the privacy problem. Start at docs.aztec.network or read the architecture deep-dive on The Best of Both Worlds: How Aztec Blends Private and Public State.